The Dark Web Mystery Explained: How the Dark Web Works in 2026.
2/02/2026
Category: Opsec
Category: News | Published: February 2, 2026
Introduction: Unmasking the Dark Web Mystery in 2026
The term “dark web” still conjures up intense images in 2026—think hooded hackers, secret marketplaces, and those hidden nooks of the internet where anything seems possible. Hollywood thrillers and sensational headlines have transformed the dark web into a kind of digital legend, often depicted as a vast underground realm that operates outside the bounds of law and reason.
The reality is far less sensational—and far more interesting.
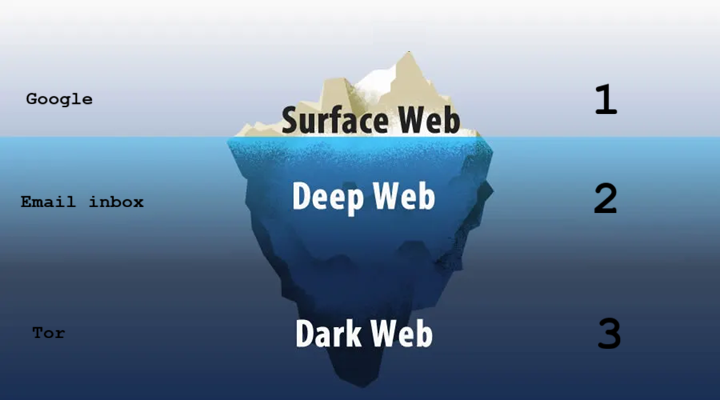
Despite its reputation, the dark web makes up an extremely small fraction of the internet, estimated at around 0.01%. In contrast, the deep web—password-protected content such as emails, banking portals, and private databases—accounts for over 90% of all online content.
In recent years, the Tor network has seen daily usage fluctuate between 2 to over 3 million users around the globe. This surge is fueled by a mix of journalists, researchers, privacy advocates, and individuals living under restrictive regimes, as well as criminals and scammers. It's this dual nature that keeps the dark web both significant and contentious..
This article, “The Dark Web Mystery Explained: How the Dark Web Works in 2026,” dives into the technology, purpose, risks, and myths that surround the dark web. You’ll discover how Tor onion routing operates, how dark web technology has progressed in 2026, what really goes on in .onion sites, how the myths stack up against the truth, and how to safely access deep web contents for research purposes.
Disclaimer: This content is educational. Accessing the dark web is legal in many countries, but engaging in illegal activity is not.
To understand how the dark web works in 2026, you first need to understand where it fits within the broader internet.
1. The Surface Web
What is the Surface Web?
The surface web is basically the part of the internet that search engines like Google or Bing can actually find and index. This includes news sites, blogs, social media, and all those public-facing websites we use every day. It’s pretty surprising, but this only makes up about 4–10% of all the content out there on the web!
2. The Deep Web
What is the Deep Web?
The deep web isn’t as scary as it sounds—it’s actually just a private space. This includes things like your email inbox, online banking sites, corporate intranets, and medical or academic databases. Basically, anything that requires a login falls into the deep web category. As of 2026, this part of the internet still makes up over 90% of the whole thing.
3. The Dark Web
What is the Dark Web?
The dark web is designed to be hidden from plain sight. To access it, you need special software, and it operates on overlay networks like Tor, I2P, or Freenet. Websites on the dark web use unique domain endings like .onion, and the traffic is routed in a way that keeps users' identities under wraps.
In 2026, the dark web remains small in size but outsized in influence—especially in discussions about privacy, cybercrime, and digital freedom. Explore unsolved dark web mysteries in 2026: real cases that continue to puzzle cybersecurity experts and OSINT researchers
The Internet Layers Explained
| Internet Layer | Description | Estimated Size |
|---|---|---|
| Surface Web | Publicly indexed websites accessible via search engines | 4–10% |
| Deep Web | Private, login-protected content such as email and banking | 90%+ |
| Dark Web | Hidden networks requiring special software like Tor | ~0.01% |
Core Technology: How the Dark Web Actually Works in 2026
The Tor Network Explained
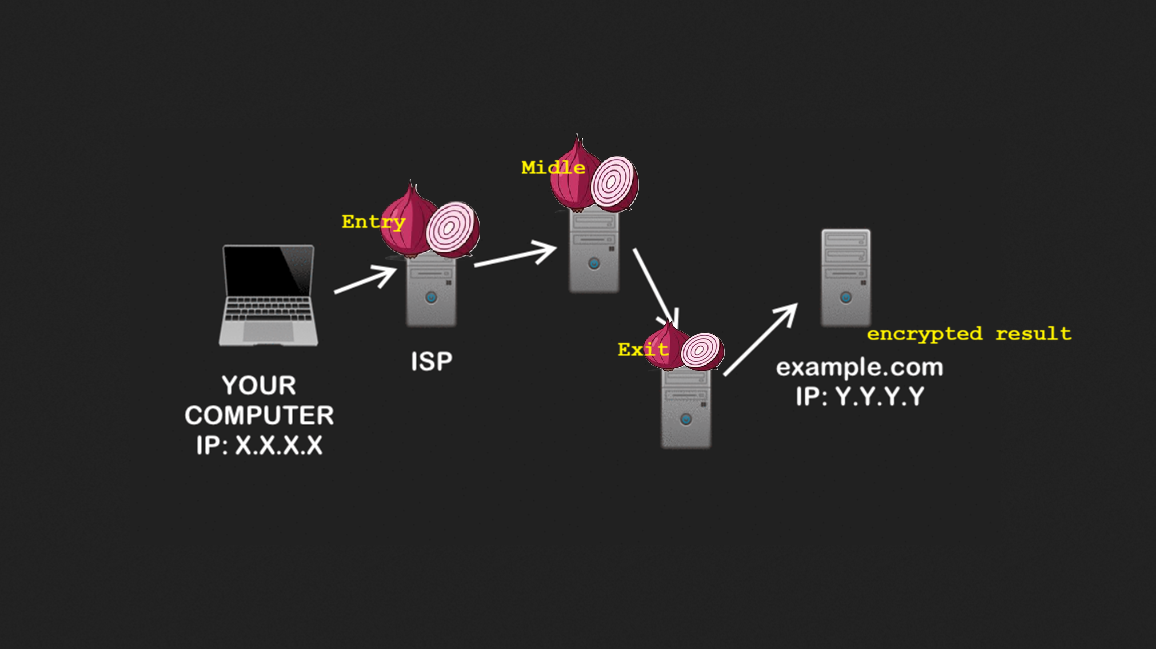
The most important answer to how the dark web works in 2026 begins with Tor, short for The Onion Router.
Tor enables anonymous communication by routing internet traffic through multiple volunteer-operated servers called relays. Each relay knows only the previous and next hop—not the entire route.
What Is Onion Routing?
Onion routing is a method used for keeping communication private and anonymous over networks like the internet. It does this by wrapping data in several layers of encryption—much like the layers of an onion—and sending it through a series of typically three volunteer-operated nodes, known as Tor relays.
Onion Routing Step by Step
- Your traffic is encrypted multiple times.
- It passes through an entry relay, middle relay, and exit relay.
- Each relay removes one encryption layer.
- No single relay knows both your identity and destination.
This layered encryption is why Tor is compared to an onion.
Hidden Services and .onion Sites
Dark web websites are called hidden services or onion services. Instead of traditional IP addresses, they use cryptographic identifiers ending in .onion.
These services are intentionally concealed within encrypted networks, keeping both the user and server anonymous. They are not indexed by search engines and never leave the Tor network.
Why Are Dark Web Websites Called Hidden Services?
Dark web websites are called hidden services (also known as onion services) because they are intentionally concealed within encrypted networks—primarily the Tor network. Their physical server locations and IP addresses are untraceable using traditional internet methods. Access requires specialized software, and these sites are not indexed by standard search engines, ensuring anonymity for both users and site operators.
How Hidden Services Differ From Regular Websites
- Both the user and the server remain anonymous
- Traffic never exits the Tor network
- There is no centralized hosting provider
Other Dark Web Networks in 2026
While Tor dominates the dark web ecosystem, several alternative networks continue to exist:
- I2P (Invisible Internet Project): Peer-to-peer tunnels used to host “eepsites”
- Freenet: Decentralized publishing and file storage network
- Lokinet: An emerging privacy network focused on routing and resilience
Tor remains the most widely used dark web network due to its usability, large user base, and continuous development.
Dark Web Technology Updates in 2026
- Improved Snowflake and WebTunnel bridges for bypassing censorship
- Enhanced defenses against traffic correlation attacks
- Growing use of artificial intelligence by both attackers and defenders
- Increased focus on post-quantum cryptography research
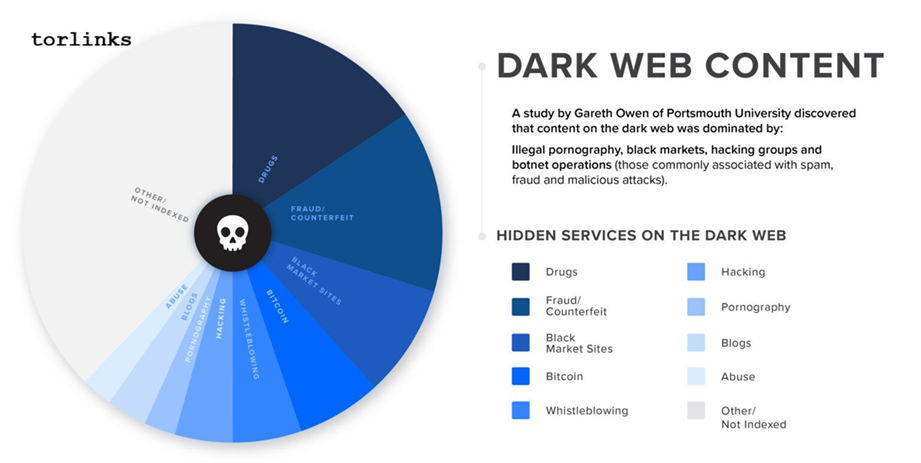
What Actually Happens on the Dark Web in 2026
Legitimate Uses
Contrary to popular belief, many dark web activities are legal and ethical. These include:
- Dark web payment monitoring
- Whistleblowing platforms for journalists
- Darknet activity mapping
- Secure communication for activists
- Circumventing censorship in authoritarian states
- Dark web data search
- Academic and cybersecurity research
- Trending dark web products for research purposes
What Actually Happens on the Dark Web in 2026
Contrary to popular belief, many dark web activities are legal and ethical:
Legitimate Uses
- Whistleblowing platforms
- Journalistic source protection
- Darknet activity mapping for investigators
- Censorship circumvention
- Academic and cybersecurity research
- Dark web data search
- Secure communication for activists
- Trending dark web products for research
The illegal side does exist:
Illicit Activity
- Data leak marketplaces
- Ransomware operations
- Underground document services
- Fraud and credential sales links
- AI-assisted phishing kits
- Counterfeit documentation services
Dark Web Myths vs Reality (2026)
| Myth | Reality |
|---|---|
| The dark web is massive | It represents less than 0.01% of the internet |
| Everyone is a criminal | Many users seek privacy and safety |
| You get hacked by visiting | Risk comes from interaction, not viewing |
| It is untraceable | Law enforcement uses advanced forensics |
The dark web mystery explained 2026 comes down to this: the danger is exaggerated, but the risks are real.
Risks, Safety, and OpSec in 2026
Key Risks
- Malware and fake downloads
- Scam marketplaces
- Law enforcement honeypots
- Underground escrow abuse
- AI-driven social engineering
- Hidden service forgery networks
Safety and Awareness Tips
- Use the official Tor Browser only
- Click only on verified darknet vendors
- Avoid sharing personal information
- Disable scripts where possible
- Verify sources and links carefully
- Use a vendor imposter detection tool such as torlinks.live
- Separate identities and devices when researching
Conclusion: Is the Dark Web Still a Mystery?
By now, how the dark web works in 2026 should feel far less mysterious. It is a small, specialized layer of the internet powered by anonymity technology and used by a wide range of people for different purposes.
Understanding the dark web—rather than being afraid of it—is crucial for staying aware of cybersecurity, enhancing digital literacy, and fostering informed conversations. If you care about privacy, technology, or online safety, the dark web isn’t just some urban legend—it’s a reflection of our online world.
Frequently Asked Questions
What is the dark web?
The dark web is a hidden part of the internet accessed through networks like Tor.
How does Tor work?
Tor uses onion routing to encrypt and route traffic through multiple relays.
Is the dark web illegal?
Accessing it is legal in many countries; illegal activity is not.
Is everything on the dark web criminal?
No. Many legitimate uses exist, including journalism and privacy protection.